Website is an important part of today’s business and having malicious content injected in website is bad for business.
Hackers are now penetrating into websites and planting hostile scripts to silently spread malware to its visitors.
This will compromise your customer’s security and privacy.
Eventually, search engines will blacklist your website.
Although the website owner is a victim himself, such events are still very bad for his business’s reputation.
The “GRED WebCheck” service for detecting online manipulation due to cyber-attacks has already been deployed by some 5,000 government agencies, local governments, and companies and been met with high praise for things like its sophisticated detection engine and ease of deployment since going on sale in 2009. IIJ Europe offers this service as SecureBrain’s sales representative in European region.
What is GRED?
Product Overview
Features
- Early warning against website malware injection, defacements and search engine blacklisting
- Monitors website 24×7
- Alert notification by E-mail
- Privided as SaaS service with no software to install
Case Study
White Paper
Early Warning System
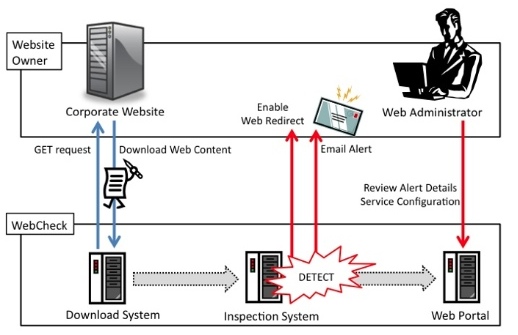
GRED WebCheck is an early warning system for website attacks.
It is a cloud-based service that continuously monitors your website 365x24x7 for the presence of malware injection and other types of malicious content.
Whenever it finds a malware threat, it will notify the website administrator by automatically sending an email.
The website administrator can then review the details on Gred WebCheck’s web portal.
Since it is a cloud-based service (SaaS), there is no hardware or software installation required on the customer’s website.
Alerting and Web Portal
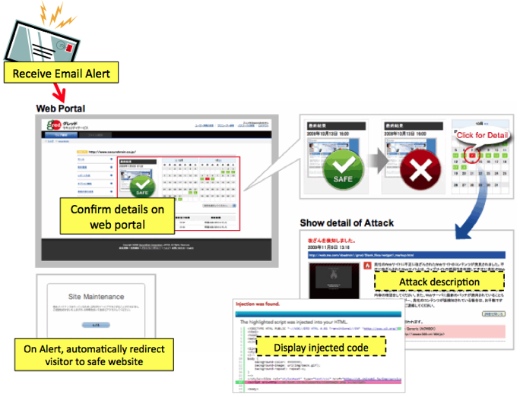
When website injection attack is identified, an email alert is immediately sent to the administrator to notify him about the threat.
The Web Portal is the mechanism responsible for taking action when a new threat has been identified in the Inspection System.
It collects enough data so that detailed information can be provided to the administrator via the Web Portal.
How it works
The administrator registers the URL of the top page of the customer’s website that needs to be monitored.
Upon registration, the system will begin deep analysis of the website.There are three main parts of the entire process.
- Download system – It navigates through the website to download its content. It will recursively crawl hyperlinks found on the website to automatically retrieve all the pages of the website that it needs to browse to.
- Inspection system – Its main function is to do a static analysis on the web content passed by the Download system to look for malicious code.
- Web portal and Action – When a malicious threat is found during analysis, the web portal takes action automatically by sending an email alert to the administrator to notify him of the problem. Depending on the pre-specified settings, it may also trigger the redirect feature on the customer’s website to automatically redirect users to a safe page upon visiting the infected website. The Web Portal also allows the administrator to view the details of the attack.
Newly Added Features
View Website Structure function
The View Website Structure function displays and visualizes the website’s link structure in a tree format based on the information collected by the GRED crawler to check for tampering. Using this function enables the viewer to visually understand the location of any detected tampering, alert, or broken link, etc., and better enables an understanding of the extent of its influence and quicker restoration. CLICK HERE for details.
Broken Link Detection function
The Broken Link Detection function detects pages whose links have been broken and displays them as a list. Only links tracked by the GRED crawler are targeted for Broken Link Detection. Any URL that returns a 404 error response from the server is considered to be a broken link. Only the latest analysis results are displayed. CLICK HERE for details.
Register Non-Linked URL function
Registering URLs that cannot be tracked from the URL on the top screen as non-linked URLs from the management screen enables them to be analyzed. Only the analysis target domains can be registered as non-linked URLs. URLs to be analyzed need to be registered one by one because links are not tracked automatically. Up to 20 URLs can be registered. CLICK HERE for details.
Port Scan Diagnosis function
Port scan diagnosis checks whether the target port is open or not simply by selecting “Port Scan” and clicking the “SCAN” button from the GRED management console. If there is a product whose vulnerability information is provided to an open port, reference information, such as the URL of the Website that provides the information is displayed.
WordPress Simple Vulnerability Diagnosis function
This function checks whether any vulnerabilities exist or not in the WordPress templates, themes, or plug-ins that are currently used with one click from the GRED management console. If diagnosed that a vulnerability exists, the vulnerable version and vulnerability details are displayed as well as showing reference information, such as the URL of a website that provides information on updates, etc.
Fees for 'GRED WebCheck'
|
Monthly |
|---|
|
240 GBP/270 EUR |
|
1 FQDN |
|
Up to 1,000URLs |
Japan Share No.1 Website Attack Detection System

Source: MIC Research Institute Ltd.
Current status and future outlook of cyber security solution market 2018
https://mic-r.co.jp/mr/01305/
SecureBrain Corporation is a cyber security specialist that brings IT security to web service providers, enterprises, and more amid diversifying online threats. This Japanese security specialist provides reliable security information, as well as high-quality security products and services as part of its vision of “contributing advanced technologies toward the creation of a more comfortable and worry-free networked society.
Security
IIJ offers multi layered security solutions designed to protect your IT environment from cybersecurity threats. All the essential security measures including GDPR compliant security minimise your impact on cyber attacks.